Mitigating Trojan Source Attacks
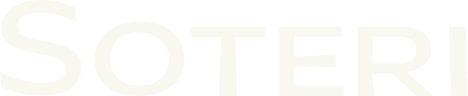
The Trojan Source Attack, tracked as CVE-2021-42574, and disclosed on , works by using invisible unicode characters used to control interpretation of text as left-to-right or right-to-left to craft malicious source code which appears to function in one way, but is compiled in another. Code which seems to be valid could be commented out.
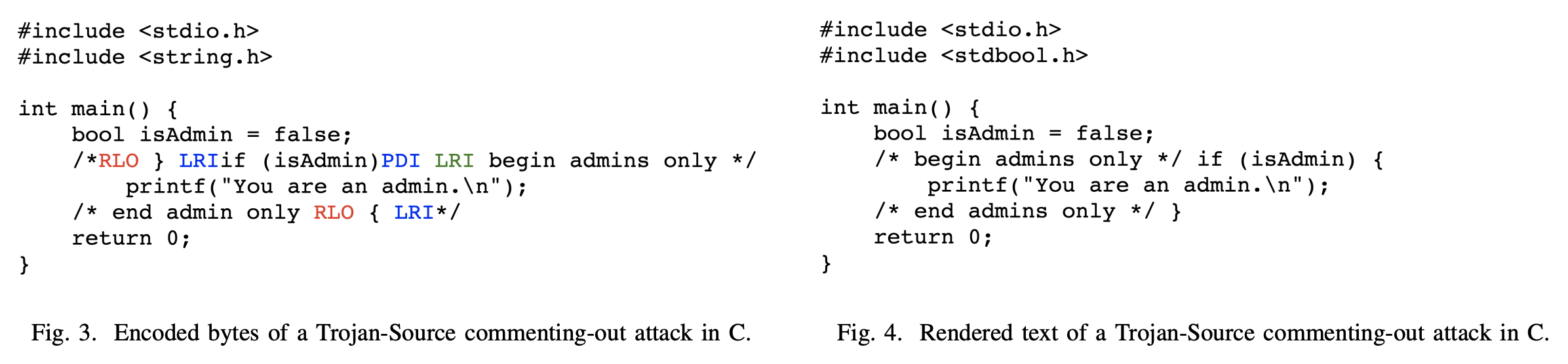
Figures 3 and 4 from “Trojan Source: Invisible Vulnerabilities” by Nicholas Boucher and Ross Anderson
Atlassian has updated Bitbucket to highlight these characters in pull requests and source code view to make it more obvious when one of these characters has been inserted into your source code: Multiple Products Security Advisory - Unrendered unicode bidirectional override characters - CVE-2021-42574.

Bitbucket’s mitigation for Trojan Source attacks highlights the hidden characters for reviewers.
But what if you want to prevent these characters from being committed, or automatically audit your Bitbucket instance for this attack? Security for Bitbucket offers a preconfigured rule to find and block these potential attacks.
Install Security for Bitbucket 3.8.0 or greater – this is the first version with the
TROJAN_SOURCErule. It is enabled by default.Run a total instance re-scan, using the
forceparameter to re-scan already scanned code with this new rule. See REST API for Mass Scanning.Turn on the Security Hook included with Security for Bitbucket to prevent new potential malicious code from being committed. See Scanning Every Push with the Security Hook for more information.
Update your Bitbucket version as recommended by Atlassian to allow for reviewers to see these characters in code reviews.
For more information on the vulnerability, you can visit Trojan Source Attacks and read the paper.