Defining Repository-Level Detection Rules
Some repositories may have specific requirements for vulnerability detection which differ from the rules defined globally.
To address repository-specific needs, you can use a per-repository configuration file. This file is committed to an individual repository and affects only the repository where it is committed. When this option is enabled, Security for Bitbucket looks for a file named soteri-security.yml in the root directory of the repository. You will need to create and commit this file yourself if the repository has no soteri-security.yml yet.
Rules and options configured in this file are used both when repository content is updated (if Soteri - Scan Commits hook is enabled) and when you trigger scans manually from the Soteri Security Scan tab of the repository.
As of version 3.10.0, this file is always loaded from the latest commit of the default branch. This ensures that scans of even historical branches are conducted with the most up-to-date configuration.
Per-repository configuration is disabled by default. The global settings page has a toggle to enable custom repository rules support:
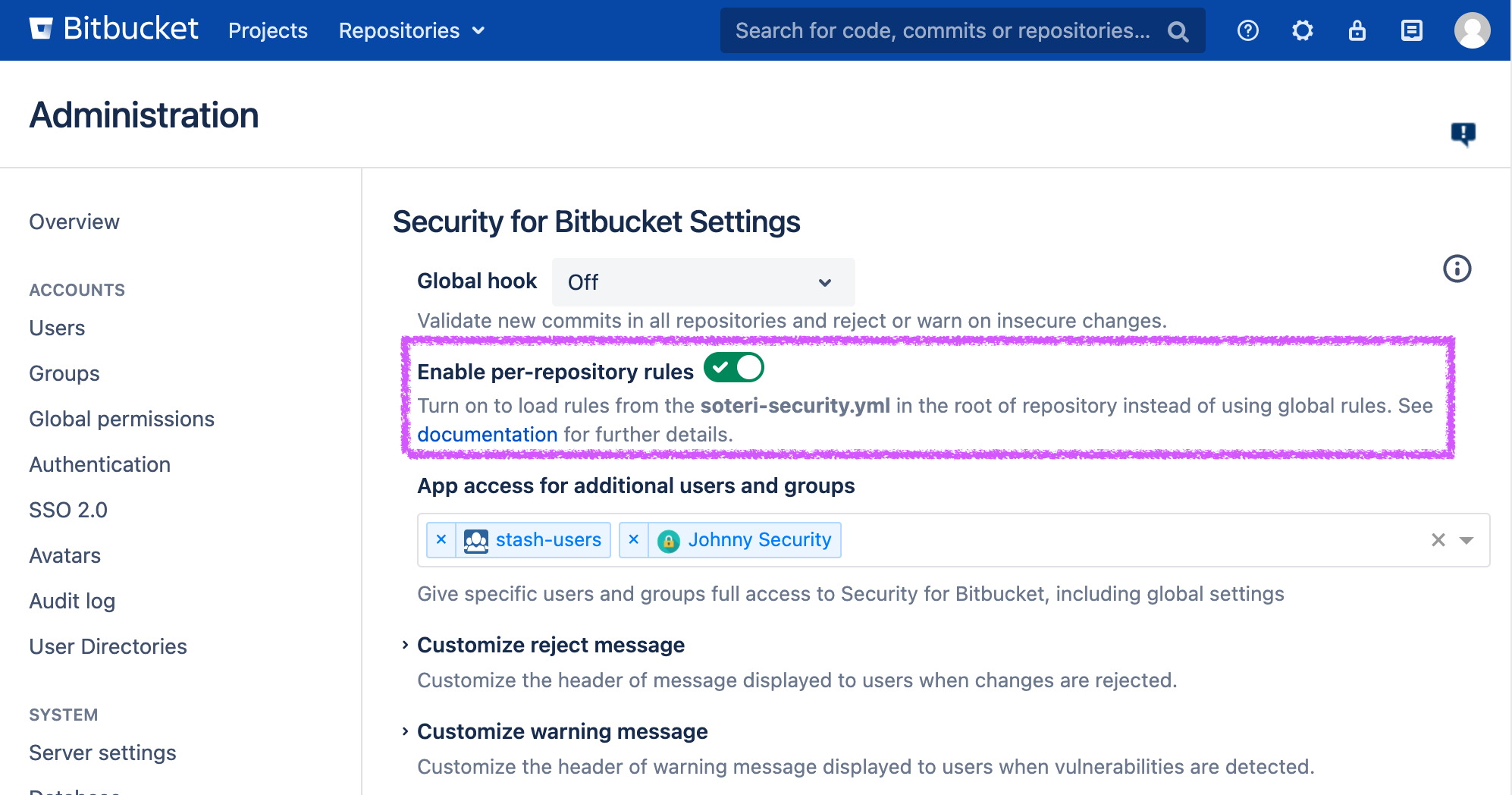
The per-repository rules toggle on Security For Bitbucket’s global settings page
Supported Configuration
This table documents all supported soteri-security.yml configuration options.
Option key | Description |
|---|---|
| Set this to false to NOT inherit built-in rules. If true, file contents are checked against globally enabled built-in rules. |
| Set this to false to NOT inherit globally defined custom rules. If true, file contents are checked against globally defined and enabled custom rules. |
| Use this field to apply a specific set of built-in rules that will always apply, regardless of Use in conjunction with Rule names can be referenced from the settings page, or Built-In Scanning Rules. |
| Use this field to define and apply your own custom rules. Rules are defined as key value pairs |
| Use this list to mark specific files or paths (using a regular expression as the value) as allowed even if they contain vulnerabilities. This can be useful for storing some non-sensitive credentials and configuration data. See more details on allow-listing here: Allow-listing Detected Secrets |
Below is an example of a soteri-security.yml config:
inherit_builtin_rules: false
inherit_custom_rules: false
rules:
- RSA_PRIVATE_KEY
- SSH_PRIVATE_KEY
custom_rules:
# Comments are supported.
BITCOIN_ADDRESS: '^[13][a-km-zA-HJ-NP-Z0-9]{26,33}$'
YOUTUBE_LINKS: '<a\s+(?:[^>]*)href=\"((?:https|http):\/\/\w{0,3}.youtube+\.\w{2,3}\/watch\?v=[\w-]{11})">(?:.*?)<\/a>'
allowlist_paths:
- config/server.yml
- (.*)\.insecurePre-Receive Hook
When Security for Bitbucket is installed and enabled, any changes which might invalidate soteri-security.yml on the default branch will be blocked by an included pre-receive hook. Changes which can be rejected must both:
Target a repository’s default branch. This includes:
Direct pushes to the default branch.
The merging of pull requests which target the default branch.
Modify
soteri-security.ymlsuch that it is no longer valid. Examples of potential reasons whysoteri-security.ymlcould be invalid:Doesn’t parse as a valid YAML. You can use online tools to check that your YAML is valid before committing, like this one.
Note that the YAML standard forbids tab characters. You must use spaces in
soteri-security.yml.
Properties don’t parse as expected (e.g.,
inherit_builtin_rulesmust be parsable as a boolean).Provided regular expressions are invalid (e.g., for
allowlist_pathsor any definedcustom_rules). You can use online tools to validate that your regexes are valid before committing, like this one.Rule names that don’t have regular expressions associated with them.