Viewing Audited Events
To help administrators keep track of various events, Security for Confluence (version 1.6.0 and later) places certain entries in Confluence’s Audit Log.
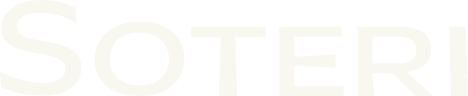
Accessing the Audit Log
From the Confluence administration page, select Audit log (under “Administration”) from the sidebar. This brings up the “Advanced audit log” page:
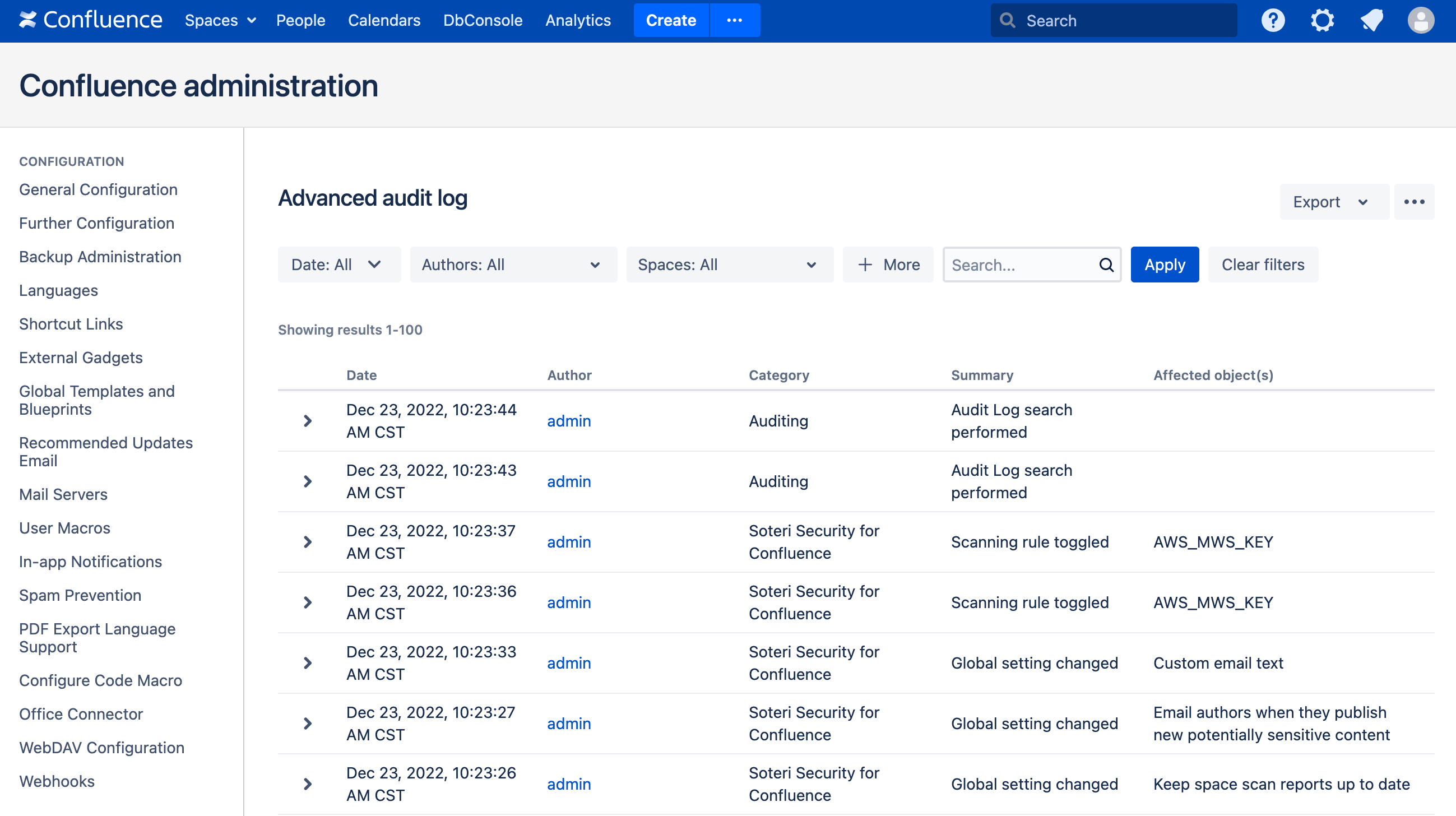
From here, click on the + More button. A new Categories drop-down will appear. From that, select “Soteri Security for Confluence” to view only Security for Confluence audit log events. You can expand events to see more details:
Audited Events
The following Security for Confluence events are currently recorded in the audit log:
Any changes to global scanning settings, including scanning rules being enabled or disabled.
Custom rule creation, updates, or deletion.
Whenever anyone manually scans a page, space, or the whole instance.
Whenever someone marks (or un-marks) a finding as reviewed.
Whenever someone publishes potentially sensitive content.
Caveat: only generated when the Keep space scans up to date option is enabled and the space has already been fully scanned by a manual trigger.
Whenever an email notification is sent notifying an author that they’ve published potentially sensitive content.
REST API
Confluence provides a REST API for accessing all audit log events. For instance, you can fetch recent audit events with a REST API call that looks like this:
curl -u admin https://{confluence.server}/rest/api/auditReference the REST API documentation for your Confluence version for more information.